The E-ISAC's 2025 Report: Real Progress, Remaining Constraints
By patrick miller
This post reads the 2025 E-ISAC report carefully and takes its numbers at face value. It also asks the follow-on question that annual reports cannot answer on their own… given the threat environment the E-ISAC describes, is the sector sharing enough back into the system for collective defense to actually work effectively? The report clearly demonstrates strong operational performance. But the sector still faces a deeper structural constraint: the organization responsible for voluntary threat sharing is housed within the same institution that enforces cybersecurity compliance. That structure shapes how much information utilities are willing to disclose and no amount of operational excellence fully overcomes it.
Overview
The E-ISAC's 2025 End-of-Year Report reflects an organization that has grown significantly in scale, sophistication, and operational output. By almost any measurable indicator, 2025 was the strongest year in the E-ISAC's history. Record conference attendance, a major jump in GridEx participation, expanded membership, and a threat intelligence operation that is genuinely useful to the utilities and operators who rely on it. These are real accomplishments worth recognizing plainly.
The E-ISAC's work is incredibly important. The bulk electric system faces a threat environment that is more complex, more adversarially capable, and more geopolitically charged than at any point in the organization's history. The people running the 24/7 Watch, producing threat hunt reports, running VISA workshops, and coordinating across government and international partners are performing a seriously valuable service for a sector that depends on them.
This post reads the 2025 report carefully and takes its numbers at face value. It also asks the follow-on question that annual reports cannot answer on their own: given the threat environment the E-ISAC describes, is the sector sharing enough back into the system for collective defense to actually work effectively? The answer to that question depends less on the E-ISAC's operational performance and more on the structural conditions it operates within.
The 2025 Report - By the Numbers
The Electricity Information Sharing and Analysis Center (E-ISAC) released its 2025 End-of-Year Report in early 2026, and the headline numbers are worthy of a write-up. This is not a small operation and 2025 was, by measurable indicators, a very strong year.
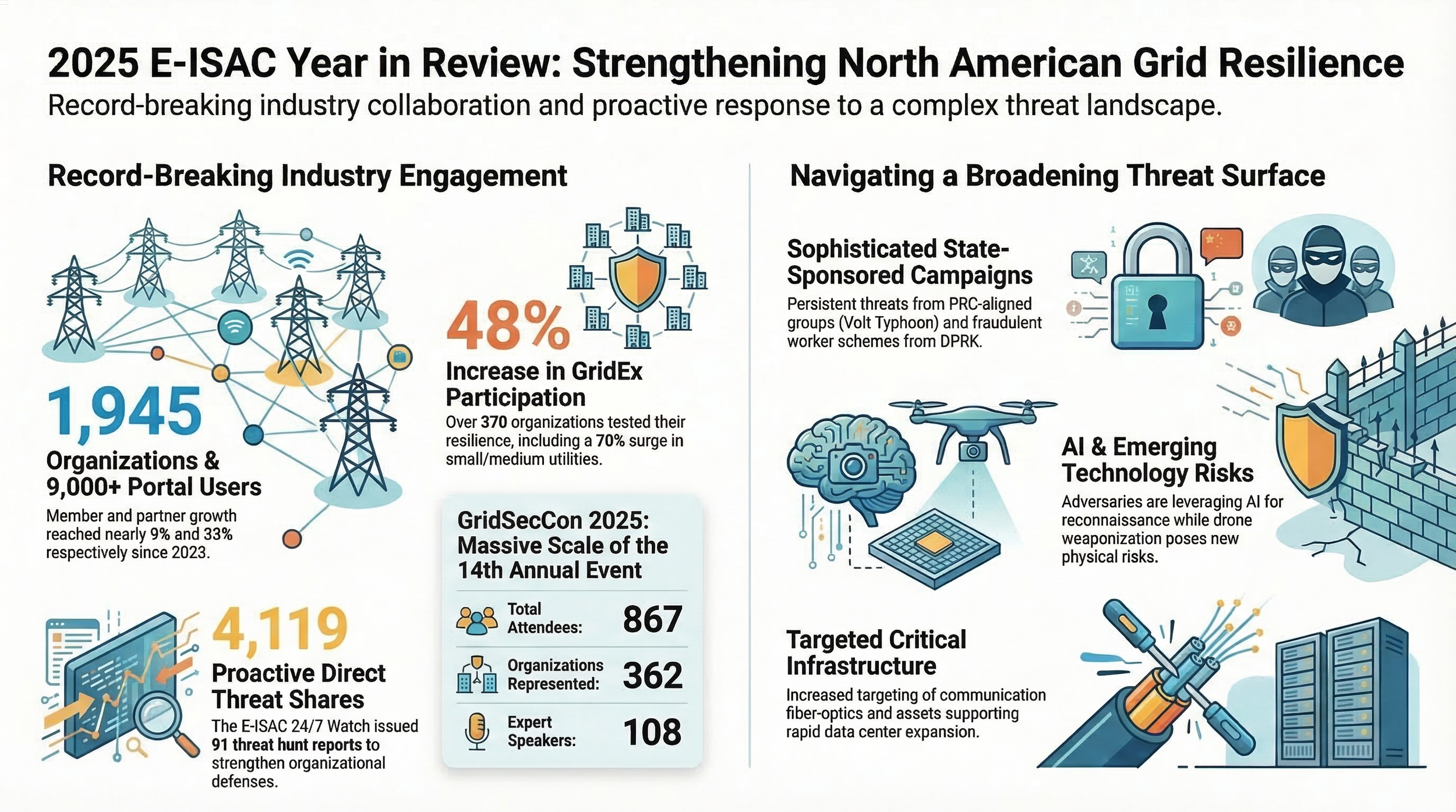
GridSecCon 2025, held in Las Vegas in October, drew 867 attendees from 362 organizations across 46 sessions with 108 speakers, 61 sponsors, and 57 exhibitors. The E-ISAC describes it as the largest and most dynamic event in the conference's history. I agree, it was a fantastic event - both in content and in networking, building on the previous years and increasingly better each time. GridEx VIII, the biennial large-scale grid security exercise, saw a 48% increase in organizational participation compared to GridEx VII, with over 370 organizations taking part. A 70% increase in participation from small and medium-sized utilities was particularly notable. Two new accessibility formats, GridEx-in-a-Box and a Tabletop Scenario option, responded directly to feedback from prior exercises and lowered the barrier to entry for organizations that previously lacked the resources to participate at scale. (Sidebar: GridEx is the one exercise in this sector with no good excuse to skip. GridEx is free, extremely well-produced and effective, it scales to your organization's size, and it stress-tests plans you will absolutely need someday. There is no credible reason not to participate).
The membership base has also grown materially. The E-ISAC now counts nearly 1,945 member and partner organizations, with member organization growth of nearly 9% and portal user growth of over 32% since 2023. Partner growth since 2023 reached nearly 25%. These are indicators of an organization that continues to expand its reach and perceived relevance within the sector.
On the threat intelligence side, the E-ISAC's 24/7 Watch issued 91 threat hunt reports, 3 All-Points Bulletins, and made 4,119 proactive direct shares to member organizations. Monthly threat briefings, Vulnerability of Integrated Security Analysis (VISA) workshops, an AI Pulse information series, and the ongoing CRISP program for real-time network traffic monitoring all continued. The E-ISAC also participated in more than 215 events during the year and testified before the House Energy and Commerce Committee's Energy Subcommittee in December.
Beyond metrics, the threat picture the report captures is substantively important. State-sponsored actors from the People's Republic of China, including Salt Typhoon and Volt Typhoon, continued sophisticated campaigns against critical infrastructure. Cyber hacktivist groups increased in number and profile. North Korean actors fraudulently applied for employment at electric utilities, introducing insider threat and supply chain risk vectors that many organizations were not positioned to screen for. Drone weaponization threats to physical infrastructure prompted the E-ISAC to stand up a dedicated Drone Working Group. These are not hypothetical risks, and the E-ISAC's work to document, analyze, and disseminate information about them provides genuine value.
The Vendor Affiliate Program grew with nine new members, and the program's report of 80% VAP member participation at GridSecCon illustrates the extent to which the E-ISAC has built a functioning ecosystem around its core information-sharing mission.
What the Numbers Cannot Tell Us
The E-ISAC's annual report is a well-produced institutional document. It reports activity and engagement with transparency. But there is a category of measurement it cannot fully address, and the gap matters: how much is the sector actually sharing about what is happening to it?
NERC's annual CIP-008-6 report, filed with FERC in March 2025 covering calendar year 2024, shows three reported incidents across the entire North American bulk electric system. All three were attempts to compromise, none resulted in disruptions to BES operations. The four-year total since CIP-008-6 took effect in 2021 is 16 reports.
What we can say with confidence, drawing on FERC's own regulatory record, is that the definitional mismatch between OE-417 and CIP-008-6 was significant enough that FERC intervened. In issuing Order No. 848 in 2018, the Commission concluded directly that the gap in reporting between what utilities disclose to DOE versus what reaches NERC "suggests a gap in the current reporting requirements" and that the existing threshold "may not reflect the true scope and scale of cyber-related threats facing responsible entities." That order created CIP-008-6. Four years of data later, the reporting totals remain in the single digits annually.
Part of this is definitional. CIP-008-6 has a high threshold. A “Reportable Cyber Security Incident” requires a malicious act or suspicious event that compromises or attempts to compromise an Electronic Security Perimeter, Electronic Access Control or Monitoring System, or Physical Security Perimeter associated with a high or medium impact BES Cyber System. The vast majority of scanning, probing, phishing, and low-level intrusion attempts that utilities experience daily does not meet that bar, and should not be expected to. What Ampyx Cyber analyzed in a March 2025 blog post on four years of CIP-008-6 data remains true: even within the reporting framework's scope, there is documented variance in how entities interpret the term "attempt to compromise." NERC acknowledged this in Project 2022-05, which is working on minimum expectation guidance for that determination.
But definitional ambiguity is only part of the explanation. The other part is structural.
[Update — March 2026]
NERC filed its 2025 Annual Report on Cyber Security Incidents with FERC on March 20, 2026, covering the fifth year of CIP-008-6 implementation. The report shows one mandatory incident report for calendar year 2025, down from three in 2024. The single reported incident involved port scans to multiple external interfaces from a single IP address in the SERC region; network perimeter controls blocked the connection, and there was no operational impact to BES reliability. The five-year total since CIP-008-6 took effect in January 2021 is now 17 reports across the entire North American bulk electric system.
What makes this filing particularly notable is NERC's own characterization of the result. The report states directly that "the diminished number of reports this year reinforces the importance of establishing criteria that does not rule out attempts to compromise from being reported simply because no harm to, or intent to harm, a BCS or systems used to support the reliable operation of the BPS was identified." That is the regulator acknowledging, in a public filing to FERC, that the current threshold is suppressing reportable activity. The structural argument this post makes did not require the 2025 data to hold. But it is worth noting that NERC's own annual report to its regulator now makes a version of the same point.
The Structural Constraint No Annual Report Can Resolve
I’ve known the E-ISAC (formerly the ES-ISAC) since it’s inception in the early 2000s (nod to Lou Leffler). Yes, it’s been around that long. The E-ISAC has always been clear and explicit about its organizational design: it is a division of NERC, funded through NERC's budget, governed by NERC's Board of Trustees, served by NERC's general counsel, and staffed under NERC's organizational structure. The E-ISAC CEO also holds the title of NERC Senior Vice President.
Full disclosure: I’ve known Michael Ball for 25 years and I can personally and professionally vouch for him being the absolute best possible person to be the E-ISAC CEO. In my opinion, you simply won’t find another person as honest, high-integrity, dedicated, and experienced.
NERC maintains what it describes as a “firewall” between E-ISAC information sharing and NERC's Compliance Monitoring and Enforcement Program (CMEP), and E-ISAC staff and CMEP staff are organizationally and physically separated.
The firewall is real. It is policy-based, procedurally enforced, and taken seriously by both sides of the organization. The problem is not that the firewall fails. The problem is that utilities' legal and compliance departments operate on the basis of institutional proximity, not internal firewalls they cannot audit from the outside.
The entities asked to voluntarily share incident data with the E-ISAC are the same entities subject to NERC CIP audits, enforcement actions, and civil penalties under the same legal authority, governed by the same board, funded through the same assessment mechanism. A utility's general counsel does not need to believe the firewall is broken to advise caution about creating documentation of security events in a system operated by the regulator. Rational institutional behavior explains most of the gap, no bad faith required.
This is not a situation unique to E-ISAC or to NERC. It is a structural observation about what it means to house an information-sharing organization inside the enforcement apparatus of the sector it serves. The water sector, oil and gas sector, financial sector, and healthcare sector have all built their primary ISACs as genuinely independent membership organizations with their own governance, their own legal entities, and no regulatory parent. That is not by accident.
NERC's 2025 budget was approximately $123 million, approved by FERC and funded primarily through mandatory assessments on load-serving entities. The 2026 total E-ISAC budget (including CRISP) is $45,181,751, up from $43,795,084 in 2025, a 3.2% increase.
Breaking that down:
E-ISAC only (excluding CRISP): $32,297,950 (up 5.1% from $30,732,391)
CRISP only: $12,883,801 (down 1.4% from $13,062,692)
On the funding side, about 75% comes from assessments, 22% from CRISP participants, and the remaining 3% from other sources including interest income, the Downstream Natural Gas ISAC partnership, the Vendor Affiliate Program, and CRISP workshop fees.
The E-ISAC sits within the Situation Awareness and Infrastructure Security program area, one of NERC's seven recognized Section 215 statutory functions. That funding model provides stability and scale. It also means that the organization supporting voluntary threat intelligence sharing from the sector is financially dependent on mandatory assessments from the same entities it asks to share voluntarily.
Calibrating Against Peer ISACs
The comparison to other sector ISACs is instructive, not as a criticism of E-ISAC's work, but as a calibration and context tool for what information-sharing maturity can look like.
The following table summarizes the key structural and operational differences across four ISACs operating in sectors that face comparable threat environments.
| ISAC | Governance | Funding Model | Members / Scale | Incident Data Reported Publicly |
|---|---|---|---|---|
| E-ISAC | NERC subsidiary; governed by NERC Board of Trustees | Section 215 mandatory LSE assessments (ratepayer-funded); CRISP participant fees; Vendor Affiliate Program revenue | ~1,945 orgs; ~9,000 portal users (North America) | 3 CIP-008-6 attempts to compromise reported in 2024 (4-year total: 16) |
| FS-ISAC | Independent 501(c) nonprofit; board elected from member CISOs (Bank of America, SWIFT, CME Group, etc.) | Tiered membership dues; no regulatory assessments | 5,000+ firms in 75 countries; global reach | Publishes annual Cyber Threat Level with regional ratings set by member Threat Intelligence Committees |
| Health-ISAC | Independent 501(c) nonprofit; member-elected board; no regulatory parent | Tiered membership dues | Thousands of health organizations globally; 15 years of operation | 8,903 incidents logged in 2025 (55% increase over 2024); 1,300+ targeted alerts issued |
| ONE-ISAC (formerly ONG-ISAC) |
Independent 501(c) nonprofit; operations supported by FS-ISAC's Global Resilience Federation | Membership dues; lean model | Energy sector focused; smaller membership base than E-ISAC | Member-driven threat submissions; no public annual incident count |
The Health-ISAC comparison is particularly striking. A sector that lacks mandatory federal cybersecurity standards equivalent to NERC CIP, and whose member organizations include hospitals with far fewer security resources than most utilities, reported 8,903 incidents in 2025 and a 55% year-over-year increase in reported activity. This is not evidence that healthcare is less secure than the electric sector. It is evidence that an independent, member-governed information-sharing organization produces very different reporting behavior than a regulator-housed one.
FS-ISAC's approach is also worth noting. Rather than publishing activity metrics, its annual intelligence product leads with a Cyber Threat Level for each global region, set in real time by Threat Intelligence Committees composed entirely of member organization security professionals. The CTL is raised and lowered publicly based on actual sector threat conditions, not institutional reporting cycles. The financial sector's new FS-ISAC CEO recently acknowledged publicly that even this model needs to evolve, which is a sign of an organization comfortable with self-critical evaluation precisely because it is accountable to its members, not to a regulator.
What This Means for Utilities, Operators, and Regulators
For utilities and operators: the E-ISAC Portal and its threat intelligence products are worth engaging with fully. The 94% of survey respondents who said E-ISAC contributed to improved security are right that the output has value. The limitation is not in consuming the E-ISAC's intelligence. It is in how much of your own operational experience you can realistically contribute back into the system, given your organization's compliance exposure.
For regulators and policymakers: the low CIP-008-6 reporting numbers are not evidence that the grid is more secure than the healthcare sector's incident data suggests its sector is. They are evidence of a reporting framework that has not yet created the right conditions for candid disclosure.
The most promising structural response to this problem is the Energy Threat Analysis Center (ETAC), led by DOE's Office of Cybersecurity, Energy Security, and Emergency Response (CESER). ETAC does something E-ISAC structurally cannot: it operates as both a classified and unclassified collaboration hub, giving energy sector operators who work on behalf of the entire energy sector genuine access to Intelligence Community analysis in a secure environment. The two organizations are designed to be complementary rather than competitive. ETAC produces; E-ISAC distributes. Industry analysts embedded at ETAC review threat intelligence in real time, assess sector-specific impact, and develop mitigations that are then shared outward through the E-ISAC and the Downstream Natural Gas ISAC to energy providers across the country. After the public disclosure of Salt Typhoon's compromise of U.S. telecommunications providers in late 2024, ETAC issued four threat memos between March and August 2025 that combined government intelligence with private sector context into specific, actionable mitigations for energy operators.
ETAC solves the classification problem. It gets better intelligence to the people who need it. It does not solve the disclosure problem. Utilities share more freely with ETAC than with E-ISAC partly because ETAC's classified setting provides legal cover that E-ISAC's proximity to NERC enforcement does not. But ETAC's outputs still reach the broader sector through E-ISAC, which means the incentive structure around voluntary reporting back into the system remains unchanged.
That said, ETAC's legislative footing has also been a recurring uncertainty. The program was funded initially through the Infrastructure Investment and Jobs Act of 2021 and operationalized as a pilot in April 2023, but it has lacked a permanent statutory home. H.R. 7305, the Energy Threat Analysis Center Act of 2026, cleared the full House Energy and Commerce Committee by a vote of 47 to 0 in early 2026, unanimous bipartisan support, but the bill has not yet passed the full House. As of this writing, ETAC is funded for FY 2026 through the Energy and Water Development Appropriations Act signed into law in January 2026, but its permanent statutory authorization remains unfinished business.
The CIRCIA mandatory reporting framework represents the other major federal lever, though it arrives with its own complications for the electric sector. NERC's ERO Enterprise formally told CISA during the rulemaking process that layering CIRCIA requirements on top of existing CIP-008-6 obligations risks creating "duplicative and inconsistent reporting requirements that would cause additional regulatory burden on electricity sector participants." CISA acknowledged the overlap in its April 2024 proposed rule, committing to work with FERC and NERC to explore whether entities subject to both regimes could satisfy both through a single report. That coordination is still unresolved. More reporting requirements do not automatically produce better threat visibility, particularly when the structural conditions discouraging candid disclosure remain unchanged.
Conclusion
The 2025 E-ISAC End-of-Year Report is worth reading. It reflects genuine institutional effort and real operational output: in threat intelligence, in GridEx, in CRISP, and in the congressional testimony that helped frame the sector's collective security posture before policymakers. The E-ISAC is doing serious work inside a structure that limits how far that work can go. Both things are true. Reading the report clearly means holding both in view at the same time, and asking how we can best use these structures for the best possible outcomes for the electric sector in North America.