Poland's Energy Sector Attack: When Cyber Sabotage Targets OT [Updated]
By patrick miller
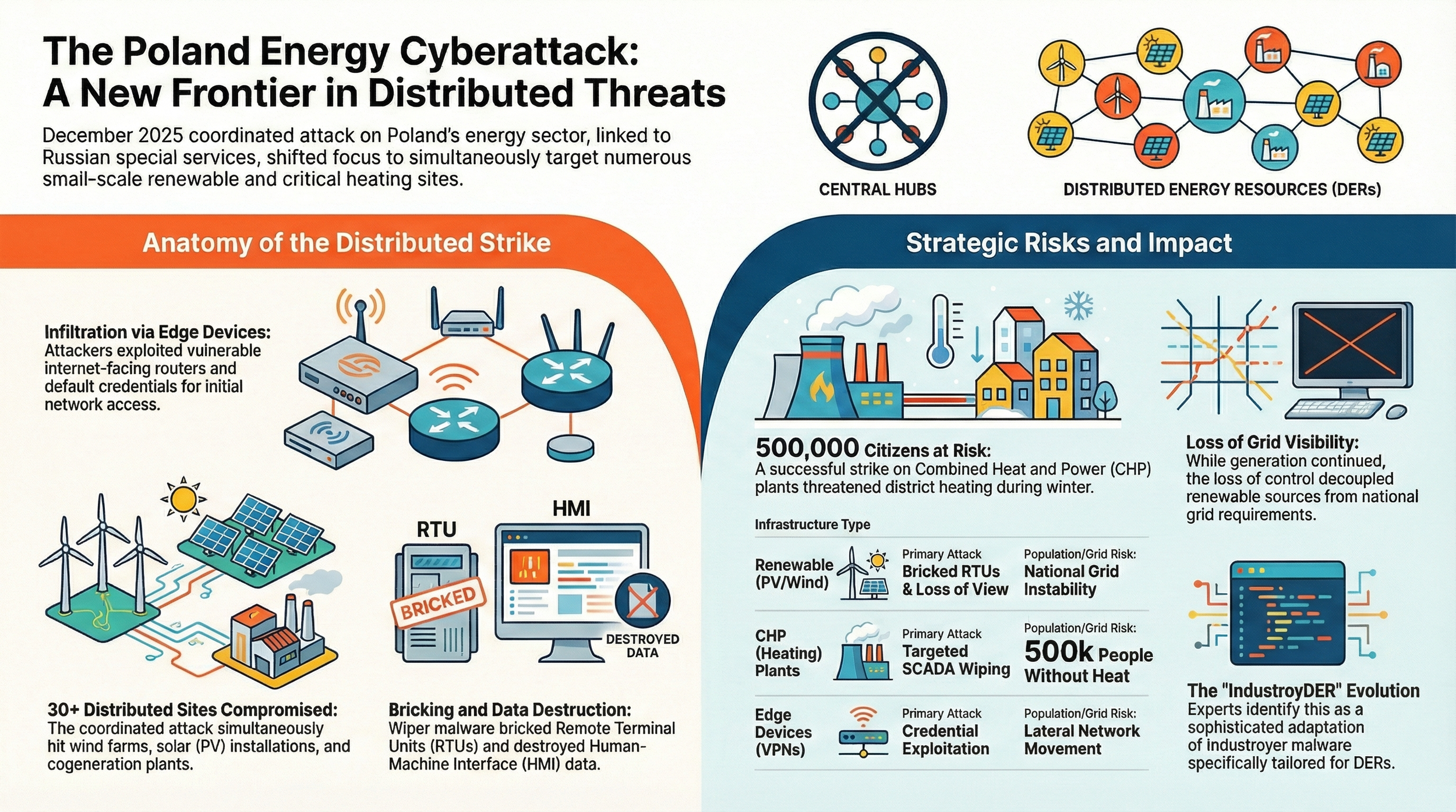
On December 29, 2025, Poland experienced coordinated destructive cyberattacks across 30+ wind/solar farms, a CHP plant, and manufacturing. Attackers exploited FortiGate devices without MFA, used default credentials on OT equipment, and deployed custom wiper malware designed to damage industrial controls. In this attack, every failure was preventable. Many of these gaps are present across North American utilities today.
Overview
On December 29, 2025, Poland experienced something the critical infrastructure security community has been warning about for years but rarely sees executed at scale: a coordinated destructive cyberattack that bridged IT and OT environments, targeting operational technology with the explicit intent to cause physical disruption. The details are officially shared in an excellent report from CERT.PL.
The attacks hit at least 30 wind and solar farms, a combined heat and power plant serving nearly half a million customers, and a manufacturing facility. This wasn't ransomware. There were no demands, no negotiations, no data theft for extortion. They came to break things. In CERT Polska’s own words: “By analogy to the physical world, [the attacks] can be compared to deliberate arson.”
What makes this incident significant is not just the coordination or the timing during Poland's winter storms, but how the attackers moved through these environments. They exploited perimeter devices, pivoted into industrial control networks, and deployed custom wiper malware designed specifically to damage RTUs, PLCs, HMIs, and serial device servers. This is the kind of attack scenario that gets modeled in tabletop exercises but rarely happens in the real world with this level of operational focus.
Credit is also due to CERT Polska and Poland's Ministry of Digital Affairs for their response and transparency. The 45-page incident report they published is one of the most technically detailed public disclosures of a destructive OT cyberattack the sector has seen. It includes forensic timelines, malware analysis with YARA rules, infrastructure IOCs, and frank assessments of what failed and why. That level of openness, especially from a nation-state target during an active geopolitical conflict, sets a standard the rest of the critical infrastructure community should follow. Simply put, CERT Polska's forensically grounded report set the bar.
The Attack Pattern
All three incidents share a common entry point: compromised FortiGate VPN appliances. The attacker gained access using accounts with default or weak credentials and no multi-factor authentication. From there, the pattern diverges based on target type, but the intent remains consistent.
At the renewable energy farms
The attacker focused on grid connection point substations, the interface between generation assets and the distribution grid. These are typically unmanned facilities with remote management capabilities. The attackers systematically damaged:
Hitachi RTU560 controllers by uploading corrupted firmware that caused boot loops
Mikronika RTUs by executing commands via SSH that deleted critical system files
Hitachi Relion protection relays using default FTP credentials to delete files required for device operation
Moxa NPort serial device servers by factory-resetting them and changing passwords and IP addresses to delay recovery
The result was loss of communication between facilities and distribution system operators. Generation continued, but visibility and remote control were lost.
At the CHP plant
The attacker had been present since at least March 2025, conducting reconnaissance of SCADA systems, exfiltrating Active Directory databases, and stealing FortiGate configurations. On December 29, they attempted to distribute wiper malware across the domain via Group Policy Objects. The organization's EDR detected and blocked the deployment, but not before the attacker also attempted to destroy server data by booting Tiny Core Linux via KVM and using dd to overwrite portions of RAID arrays.
At the manufacturing facility
The attacker used similar tactics: FortiGate compromise, lateral movement via Impacket, credential harvesting, and attempted wiper deployment via GPO. They also configured FortiGate scripts to periodically exfiltrate administrator passwords and weaken security settings, sending results to a Slack channel under their control.
What Actually Got Damaged
The technical details matter because they show how an attacker with OT knowledge operates differently than one focused purely on IT disruption.
The wiper malware (CERT Polska calls it "DynoWiper") was not designed to encrypt or ransom. It was designed to overwrite files at pseudorandom offsets, corrupt firmware, and render devices unbootable. It avoided certain system directories to prevent immediate blue-screens, allowing it to run longer and damage more files before triggering alerts.
At renewable farms, the attacker knew which devices control what. RTUs provide telemetry and supervisory control. Protection relays detect faults and isolate equipment. Serial device servers bridge legacy protocols to IP networks. Damaging all three simultaneously removes visibility, control, and protection, forcing operators into manual mode or complete shutdown.
The attacker also understood the role of default credentials in industrial environments. Hitachi RTU560 devices shipped with a "Default" account that had firmware upload privileges. Moxa NPort devices had default web credentials. Hitachi Relion relays had default FTP accounts that, if not disabled during deployment per manufacturer guidance, provided filesystem access. These aren't zero-days. They're configuration/design failures that are endemic in OT.
Attribution and Infrastructure
CERT Polska's analysis links the attack infrastructure to activity clusters publicly known as "Static Tundra" (Cisco), "Berserk Bear" (CrowdStrike), "Ghost Blizzard" (Microsoft), and "Dragonfly" (Symantec). These names refer to Russian state-aligned threat actors with a long history of targeting energy infrastructure.
The attackers used compromised VPS servers and Cisco routers for command and control, consistent with prior reporting on this actor's use of compromised infrastructure for anonymization. They also employed reverse SOCKS proxies and Tor to further obfuscate their origin.
Interestingly, CERT Polska notes that while the wiper malware shares some architectural similarities with tools historically used by the "Sandworm" activity cluster (also Russian-aligned, responsible for Ukraine grid attacks), the overlap is not strong enough for high-confidence attribution. What is clear is that this attack represents a significant escalation in publicly observed destructive cyber operations targeting European critical infrastructure.
What the Global Energy Sector Should Take From This
This is not theoretical. This fact should not be news to anyone paying attention (see Ukraine 2015, 2016, 2022). This particular attack demonstrated that adversaries are willing and able to:
Operate in OT environments with specific technical knowledge of RTUs, protection relays, SCADA protocols, and grid architecture
Maintain long-term persistent access before executing destructive actions (the CHP plant attacker was present for at least nine months)
Coordinate across multiple targets simultaneously to maximize operational impact
Exploit default credentials and weak perimeter defenses as primary entry vectors
The good news is that none of the techniques used here are novel or undetectable. Every single phase of this attack could have been disrupted with controls that already exist and are well understood:
Multi-factor authentication on all remote access, especially VPN concentrators and jump hosts
Elimination of default credentials in OT devices during commissioning
Network segmentation to prevent lateral movement from IT into OT and create control points for better monitoring
Endpoint detection and response (EDR) deployed in OT environments (where operationally feasible)
Firmware integrity verification and code signing for RTUs and controllers
Asset inventories that include serial device servers, protection relays, and other "low-visibility" devices
The CHP plant's EDR stopped the wiper deployment. That control worked. The renewable farms had no EDR on HMI computers and no monitoring on controllers. Those environments were defenseless once the attacker gained network access.
NERC CIP Roadmap Timing and Intersection
This isn’t just a Poland issue. This adversary (at the national level) is known for cyber attacks and cyber espionage in most corners of the globe - including North America.
Three weeks after the Poland attacks (but before any official report was available from CERT Polska), NERC published its Critical Infrastructure Protection Roadmap, a comprehensive assessment of where the CIP standards are failing to keep pace with how the grid has changed and how adversaries now operate. Reading the Roadmap alongside CERT Polska's incident report is forshadowing, because the Roadmap essentially predicted what just happened.
NERC's risk assessment ranked "Insufficient Low-Impact Security" as the 12th highest residual risk to the North American bulk power system. The Roadmap explicitly warned that "coordinated attacks on multiple low-impact assets could aggregate to a negative BPS impact." Poland's renewable energy farms, 30+ wind and solar facilities hit simultaneously, are exactly that scenario playing out. These were not similar to high-impact, CIP-covered control centers. They were distributed generation facilities that, if they were in the US, would not have enforceable minimum security baselines to defend against this.
The Roadmap also identified "Unregistered 3rd-Party Operators" as the 17th highest risk, noting that "non-NERC registered entities with remote access to generation facilities for monitoring, maintenance, or control capabilities could be targeted via cyber-attacks leading to risk to the grid." In Poland, the manufacturing facility attack involved FortiGate persistence scripts that exfiltrated credentials to a Slack channel, evidence of third-party operational dependency on remote access infrastructure that was never designed with adversarial resilience in mind.
NERC's top near-term recommendation is to mandate MFA for interactive remote access to low-impact BES Cyber Systems. Every entry point in Poland's attacks involved compromised remote access without MFA. FortiGate VPNs, default credentials, credential reuse, and static passwords provided the initial footholds that allowed attackers to move from IT networks into OT environments and from one facility to another across flat, under-segmented networks.
The Roadmap's second major theme, foundational cyber hygiene, reads like an autopsy checklist for what failed in Poland. NERC calls out persistent gaps in asset identification, configuration management, vulnerability and patch management, and network topology documentation. Poland's attackers exploited default credentials on Hitachi RTUs (the "Default" account with firmware upload privileges), Mikronika devices (default root SSH access), Moxa serial servers (factory default admin passwords), and HMIs (default Windows admin credentials). These are not zero-days. They are deployment failures that could have been prevented with disciplined commissioning processes and asset lifecycle management, the exact "foundational controls" NERC now says must become part of the baseline for low-impact systems.
NERC's third priority, protection of public network communications, also intersects with this attack. The Roadmap warns that "electric utilities rely on leased or third-party network circuits for SCADA and AGC communications" and that "recent state-sponsored campaigns targeting telecommunications providers demonstrate that these networks cannot be assumed to be trustworthy." While CERT Polska did not detail the telecom dependencies involved in Poland's grid operations, the attacker's use of compromised infrastructure, Tor nodes, and reverse proxies to obscure command-and-control traffic suggests they understood how to exploit trust assumptions in carrier networks. NERC's recommendation to expand CIP-012 protections to facility-to-control-center links is directly aimed at closing this exposure.
The timing here is not coincidental. NERC did not write the Roadmap in response to Poland. The Roadmap was the product of a year-long risk assessment process that surveyed industry, analyzed incident data, and built a structured evaluation framework. What makes this moment significant is that a major European grid attack, executed by a capable adversary with OT-specific knowledge, has now validated nearly every high-priority gap NERC identified.
For North American utilities, this is a forcing function. The CIP Roadmap is no longer a planning document. It is a checklist of things adversaries are already exploiting in the wild. MFA for remote access is not a future nicety, it is the control that stops the initial access phase of attacks like this. Foundational cyber hygiene is not compliance overhead, it is the difference between an attacker spending nine months undetected in your network versus being stopped at the perimeter. And low-impact system security is not optional, it is the new front line, because that is where the grid's operational dependency now sits.
The NIS 2 Question
Poland's attacks occurred during regulatory limbo, the EU's NIS 2 transposition deadline passed in October 2024, but Poland's implementing/transposing legislation remains pending in Parliament as of this writing. At the time of the attacks, Poland was still operating under the original 2016 NIS Directive.
NIS 2 brings meaningful improvements that could reduce the likelihood and impact of attacks like these: mandatory supply chain security assessments that would force scrutiny of vendor remote access practices, enhanced incident reporting requirements that drive detection capabilities and response coordination, and explicit business continuity obligations that push entities to prepare for loss of visibility and control scenarios.
The defensive successes in Poland, EDR blocking wiper deployment, operators maintaining control through SCADA loss, rapid multi-entity coordination, reflect the kind of organizational discipline that NIS 2's risk management framework is designed to institutionalize.
The Bigger Picture
Poland's experience is not unique. It is part of a pattern of increasing willingness by state actors to use cyber capabilities for coercive and destructive purposes against critical infrastructure. Ukraine has experienced repeated grid attacks since 2015. The U.S. grid has been quietly pre-positioned by Chinese actors (Volt Typhoon). European energy operators have been targeted by Russian actors for years.
What was clearly demonstrated here is that the attacks were overt, destructive, and operationally focused. The attackers were not positioning for future contingencies. This was straight sabotage.
For utilities, generators, grid operators, and all the grid assets in between and adjacent, this means that cybersecurity for OT is no longer optional, deferred, or ignored. The threat is not hypothetical. The techniques are proven. Each attack is practice for being more effective at the next one. The targets are clear and well-studied. The adversaries are mapping the environment, stealing credentials, honing skills, and preparing for the next operation. Accepting this reality and acting accordingly is the most responsible approach - regardless of whether or not you are required by regulation to do so.
Update (February 9, 2026):
Truesec
Truesec published additional analysis confirming this attack represents DragonFly/Ghost Blizzard's first known destructive cyberattack. The threat actor, assessed to be FSB Center 16, has been active since at least 2010 but previously limited operations to espionage and pre-positioning. Truesec notes that DragonFly has deliberately avoided participating in destructive attacks against Ukraine, likely because their strategic mission is to maintain the capacity to strike NATO critical infrastructure when directed. This makes the Poland attacks a significant threshold crossing, not just for Poland, but for the broader security posture of European and Nordic critical infrastructure. Truesec has released YARA rules and threat hunting queries to help defenders identify similar intrusions and wiper variants before they execute.
ESET
ESET published a detailed technical analysis of DynoWiper, attributing the attack to Sandworm (GRU) with medium confidence, a different attribution than CERT Polska's assessment linking the infrastructure to DragonFly/Ghost Blizzard (FSB Center 16). ESET's analysis reveals the attackers deployed three DynoWiper variants on December 29th alone, with PE timestamps showing iterative development: an initial version compiled December 26th, followed by two rebuilt variants on the day of the attack after earlier versions failed. All three were blocked by ESET PROTECT EDR before they could execute.
ESET highlights symbolic timing: the attacks occurred on the 10th anniversary of Sandworm's December 2015 BlackEnergy operation against Ukraine's grid, the first malware-caused blackout in history. ESET connects DynoWiper to their recently-discovered ZOV wiper used against Ukrainian targets, noting strong TTP overlaps including similar file-wiping logic and Group Policy deployment methods. However, ESET acknowledges an anomaly, Sandworm has historically operated covertly in Poland for espionage purposes, not destructively, and suggests "the preparatory stages leading up to the destructive activity may have been conducted by another threat actor group collaborating with Sandworm."
The attribution split between CERT Polska (FSB-aligned DragonFly) and ESET (GRU-aligned Sandworm) may reflect operational collaboration between Russian intelligence services or the challenges of attribution when attack infrastructure and TTPs overlap across multiple threat groups. What remains undisputed: this was a Russian state-sponsored destructive attack on NATO energy infrastructure, and EDR in OT environments stopped the wiper from achieving its intended impact.
Update (February 10, 2026)
Midnight Blue
Midnight Blue published a detailed technical analysis of the bricking TTPs used in the Poland attacks, revealing important operational and strategic implications. The Hitachi Relion IED attacks appear to match CVE-2024-8036, a vulnerability Midnight Blue discovered in ABB equipment (Hitachi acquired ABB's Power Grids division in 2020). The malicious RTU560 firmware used 240 bytes of 0xFF at the program entry point, an ARM32 undefined instruction sequence that causes infinite bootloops, rendering devices unrecoverable without physical replacement.
Midnight Blue distinguishes between "soft-bricking" (recoverable via factory reset or local interface) and "hard-bricking" (requires manufacturer return or extreme measures like JTAG). Most of the Poland attacks were hard bricks. The strategic significance: online distributors typically stock only 10-few dozen spare RTUs, IEDs, and serial converters compared to thousands of enterprise IT equipment units. Lead times for replacement can stretch to months, during which affected facilities remain non-operational. This means bricking OT equipment allows attackers to scale cyber-physical attack impact from hours to weeks or months, a force multiplier that conventional IT wipers cannot achieve.
Midnight Blue also highlights an emerging TTP: flash cycle exhaustion attacks that deliberately rewrite flash memory continuously to destroy it permanently, making even ROM bootloader recovery impossible. This technique was observed in the 2024 FUXNET malware targeting Moscow water infrastructure sensors. For defenders, the takeaway is clear: bricked embedded devices cannot be recovered remotely, and the supply chain cannot absorb sudden demand spikes. Asset inventories, commissioning discipline, and secure firmware update processes are not optional controls, they are the difference between rapid recovery and prolonged operational blackouts.
CISA & DOE CESER
CISA and DOE's Office of Cybersecurity, Energy Security, and Emergency Response (CESER) issued an official alert amplifying CERT Polska's incident report and translating the Poland attacks into direct guidance for North American energy sector stakeholders. The alert emphasizes three critical gaps that enabled the attacks: vulnerable internet-facing edge devices (CISA specifically references Binding Operational Directive 26-02 on end-of-support devices), OT equipment lacking firmware verification capabilities that allowed permanent damage, and default credentials that are not vendor-specific problems but systemic deployment failures across the sector.
CISA's explicit guidance is that operators should "immediately change default passwords and establish requirements for integrators or OT suppliers to enforce password changes in the future" and that "cyber incident response plans account for inoperative OT devices to mitigate prolonged outages." This second point acknowledges the hard truth from the Poland attacks: some bricked devices cannot be recovered remotely or quickly. Incident response plans that assume all equipment can be restored via backup and reimage are dangerously incomplete for OT environments. The US government is now telling energy sector operators that firmware-level compromise and device replacement scenarios must be part of their planning, because adversaries have demonstrated both the capability and intent to permanently destroy industrial equipment at scale.
Ruben Santamarta (NeutronMode)
Independent security researcher Ruben Santamarta published an eight-part technical analysis examining the Poland attacks from the power grid perspective rather than the OT forensics angle. Using publicly available data from Poland's TSO (PSE) and European transparency platforms, Santamarta identified measurable physical impact on the transmission network that aligned with the timing of the attacks. On December 30th, PSE issued unusual non-market redispatch orders totaling 1.2 GW against wind generation and 3 MW against solar during peak hours, significantly higher than typical operational patterns. On December 29th at 11:15, Poland disconnected from PICASSO (Europe's automatic frequency recovery reserve coordination platform) for three hours with the reason listed as "unknown," during which PSE activated downward balancing reserves to counter upward wind generation deviations.
Santamarta's analysis suggests the attackers weren't simply trying to disconnect DERs from the grid, but rather to decouple generation from grid requirements while plants continued operating autonomously. This created uncontrolled generation that forced TSO intervention to prevent congestion and imbalance. He connects this to patterns observed during the 2025 Iberian blackout, where massive DER malfunctions on the distribution side cascaded to impact the transmission network, the first time voltage-driven disconnections caused a blackout in Continental Europe's synchronous area. The spatial distribution of Poland's wind farms matters: they're concentrated in provinces with lower synchronous generation, creating asymmetric vulnerability similar to what occurred in Spain's Andalusia region during the blackout.
Most significantly, Santamarta notes the attackers demonstrated capabilities "one step away" from manipulating reactive power flows to shift parts of the grid from inductive to capacitive behavior, a far more sophisticated attack than simple circuit breaker manipulation. This reactive-based approach could cause partial blackouts without requiring massive target counts or highly sophisticated payloads, while offering plausible deniability since failures could be attributed to "improper crisis management" rather than deliberate attack. His conclusion: "weaponizing DERs' spatial distribution and reactive power characteristics" represents a new attack surface for European grids that goes beyond traditional substation-focused operations. The fact that Poland's grid withstood this is reassuring. The fact that we're now analyzing this scenario as totally plausible is the new normal for European critical infrastructure defense.