Is Something Weird Happening on Your System?
BY TERRI KHALIL
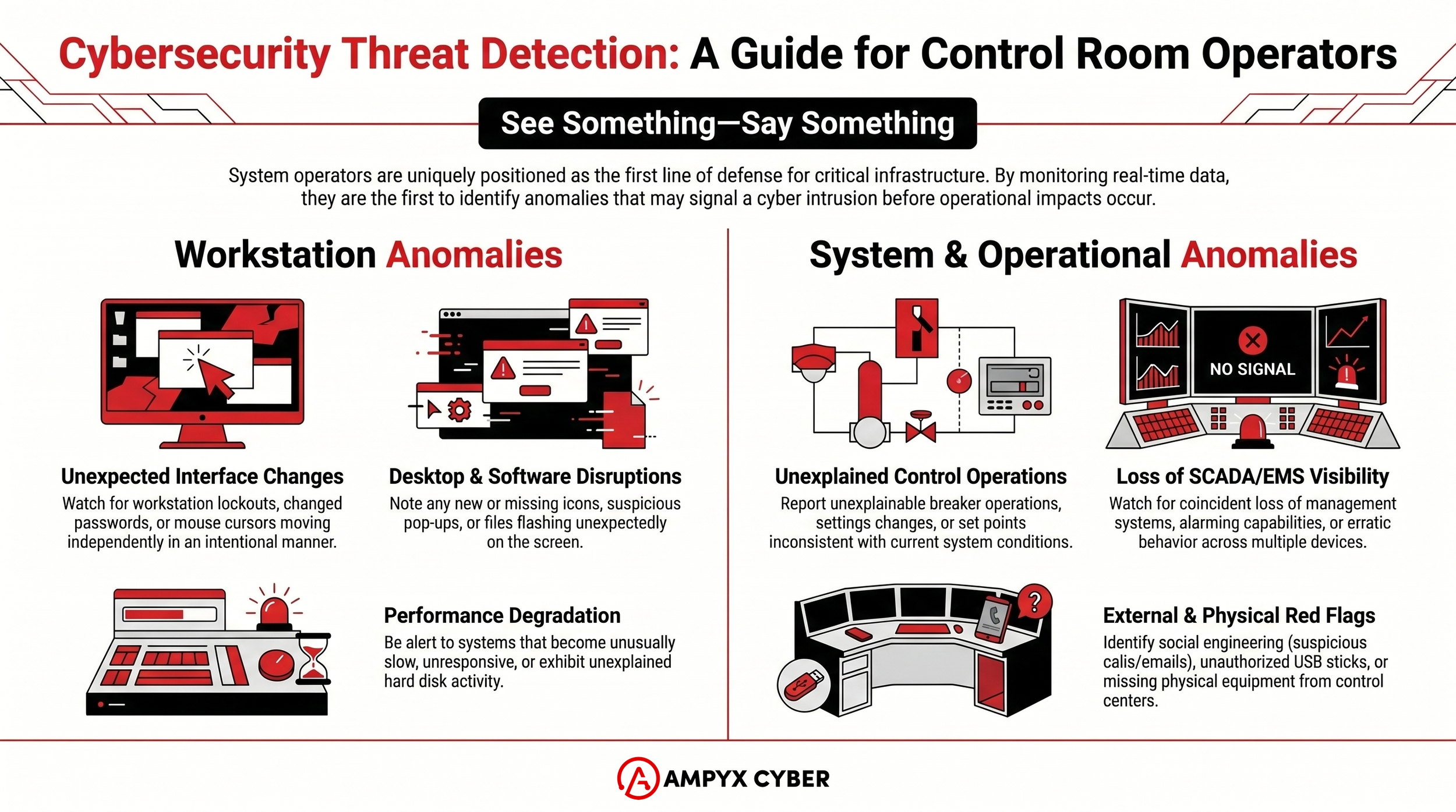
Learn how critical infrastructure operators can spot the early signs of cyber intrusions directly from the control room. Our updated guide details specific physical hardware, workstation, and SCADA anomalies to watch for. Empower your frontline staff with a proactive "See Something, Say Something" cyber defense strategy tailored for OT environments.
You may remember our recent article Proactive Cyber Defense: Recognizing Cyber Intrusions for Critical Infrastructure System Operators. It emphasized various guidelines, especially the NERC Reliability Guideline: Cyber Intrusion Guide for System Operators, Version 2. As a refresher, this document emphasizes the unique position of system operators to recognize cyber threats.
“System Operators are uniquely positioned to recognize cyber threats to the BES [Bulk Electric System]. Through direct access to Cyber Assets, and direct contact with field personnel, System Operators may be the first to recognize real-time threats to system security. They may also be targets of social engineering attempts. System Operators are potentially the first to be able to recognize early indicators of malicious cyber activity, and the last to be able to detect such activity before impacts to operations occur.”
< DOWNLOAD THE POSTER SET HERE
The NERC guideline is a quick read, and could easily be applied to many critical infrastructure sectors, or even more broadly to most Industrial Control Systems (ICS). The information is straightforward to incorporate into existing operator training, security awareness training, and/or incident response training. Our free poster set is available (intended to be posted together in multiple areas such as a control room and/or associated break room) based on the reliability guideline and slightly broadened to be applicable to any control system.
The Unique Role of the Operator System operators are uniquely positioned to recognize cyber threats. Through direct access to cyber assets and constant contact with field personnel, operators may be the first to recognize early indicators of malicious activity, and potentially the last line of defense before physical operational impacts occur.
Quick Look: What to Watch For
Below is a quick list of anomalies to focus strictly on what operators would observe directly at their consoles or within the control center. Drawing from our analysis of the NERC Reliability Guideline: Cyber Intrusion Guide for System Operators and cross-sector incident response guidance from the EPA and CISA, here are the key indicators of a potential cyber intrusion:
Physical and Hardware Anomalies in the Control Room
Unauthorized devices: Discovering unrecognized hardware, such as USB sticks, wireless access points, or new keyboards, mice, or anything new/unexpected plugged in whatsoever.
Missing equipment: Recognizing that operational devices or components are missing from the control center.
Facility system failures: Coincident loss of operational support systems at the control center, such as HVAC, fire suppression, phone/communications, or Physical Access Control Systems (PACS).
Workstation and HMI Anomalies
"Ghost" inputs: The pointer or mouse cursor moving by itself in an intentional manner to perform a task, rather than just random movement.
Unexpected lockouts: A workstation suddenly locking out or displaying a message indicating that the password has been changed.
Screen anomalies: Files or messages flashing, suspicious pop-ups appearing, or expected applications/icons suddenly appearing or disappearing from the desktop or start menu.
System performance & restarts: A system becoming unusually slow or unresponsive, exhibiting unfamiliar network data transfers, or undergoing unexpected shutdowns and reboots.
Security alerts: Anti-malware application warnings or firewall alerts popping up directly on the System Operator Human Machine Interface(s).
Account anomalies: User account authentication requests at atypical times or systems, unprompted changes in user privileges, or sudden account lockouts.
SCADA, EMS, and Operational Disruptions
Loss of control or visibility: Complete loss of SCADA capabilities that support real-time operations, automated treatment, or distribution processes.
Loss of management systems: Coincident loss of multiple EMS or SCADA components, such as alarming, ICCP connectivity, state estimation, or contingency analysis.
Unexplainable operations: System actions that are inconsistent with current conditions. In power systems, this might be unexplained breaker operations, transformer tap changes, or AGC set points. In water systems, this could be the unprompted opening and closing of valves, overriding of alarms, or disabling of pumps.
Telemetry issues: Multiple suspicious telemetry point values that contradict normal system conditions, or calls from data partners attempting to verify suspicious data they are receiving from your system.
Erratic behavior: Control system equipment acting erratically or degrading in performance, especially when more than one device exhibits the exact same behavior.
Targeted Social Engineering
Suspicious inquiries: Telephone or email requests specifically asking for information about technical systems, operational procedures, or for remote access.
Taking Action
This streamlined Quick Look is straightforward to incorporate into existing in-house training and awareness material for operators and OT support personnel, as well as incident response drills. To empower your frontline staff, we highly recommend printing and placing visual reminders directly in control rooms and associated break areas. You can easily do this by downloading and printing our Cybersecurity Threat Detection Infographic alongside our free "See Something, Say Something" poster set. These visual aids are grounded directly in the NERC Reliability Guideline: Cyber Intrusion Guide for System Operators and adapted for broader OT environments. For a detailed Deep Dive into how to recognize possible malicious actors and what to do about it, see our original, full-length post, Recognizing Cyber Intrusions for Critical Infrastructure System Operators.